Leaky Bucket Is Used For . the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. Step 1 − let us. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network.
from botpenguin.com
the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. Step 1 − let us.
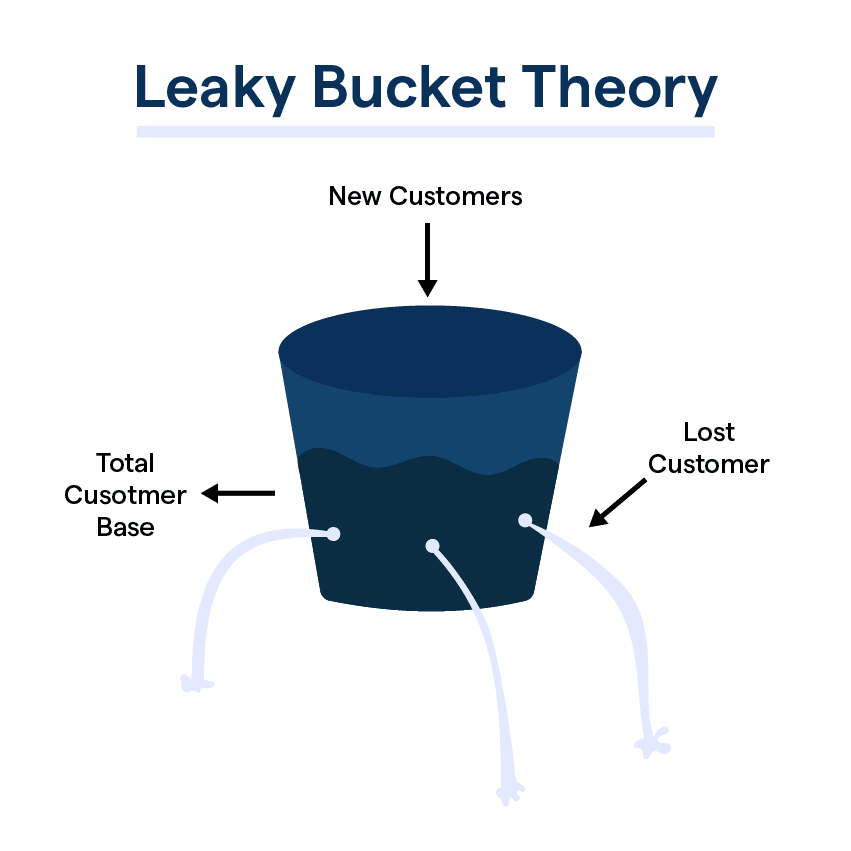
What is Leaky Bucket Theory & its Applications?
Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. Step 1 − let us.
From www.alamy.com
leaking bucket of water Stock Photo 5155466 Alamy Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data. Leaky Bucket Is Used For.
From www.studocu.com
Leaky Bucket Algorithm Leaky Bucket A leaking bucket is a simple Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets.. Leaky Bucket Is Used For.
From www.cyberthreat.report
Leaky Buckets in 2022 Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. Step 1 − let us. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily.. Leaky Bucket Is Used For.
From www.alamy.com
Studio shot of leaking bucket Stock Photo Alamy Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data. Leaky Bucket Is Used For.
From www.engati.com
What to do about your company's leaky bucket Engati Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket stock image. Image of waste, running, holes 5839431 Leaky Bucket Is Used For the use of the leaky bucket shapes the input traffic to make it conform to this commitment. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. Step 1 − let us. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the. Leaky Bucket Is Used For.
From www.slideshare.net
DON’T FILL A LEAKING BUCKET Leaky Bucket Is Used For the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket stock image. Image of waste, running, holes 5839431 Leaky Bucket Is Used For Step 1 − let us. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily.. Leaky Bucket Is Used For.
From www.coopersolutions.co.uk
leakingbucket Cooper Solutions Leaky Bucket Is Used For the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. Step 1. Leaky Bucket Is Used For.
From www.martinkentish.com
Leaky Bucket Martin Kentish Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets.. Leaky Bucket Is Used For.
From redrouteinternational.com
How leaky is your bucket? RedRoute International Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data. Leaky Bucket Is Used For.
From www.allbusiness.com
Patching the Leaky Bucket How Powerful CRM Data Can Reduce Customer Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data. Leaky Bucket Is Used For.
From theleaninnovator.net
Leaky Buckets The Lean InnovatorThe Lean Innovator Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets.. Leaky Bucket Is Used For.
From botpenguin.com
What is Leaky Bucket Theory & its Applications? Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a. Leaky Bucket Is Used For.
From www.slideserve.com
PPT Bandwidth Management PowerPoint Presentation, free download ID Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. Step 1 − let us. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control. Leaky Bucket Is Used For.
From www.researchgate.net
Leaky bucket approach. Download Scientific Diagram Leaky Bucket Is Used For the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket. Leaky Bucket Is Used For.
From www.slideshare.net
Leaky bucket algorithm Leaky Bucket Is Used For the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is. Leaky Bucket Is Used For.
From www.bigstockphoto.com
Leaky Bucket Image & Photo (Free Trial) Bigstock Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. The leaky bucket algorithm is. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket with Water Isolated Stock Image Image of hole, isolated Leaky Bucket Is Used For The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network.. Leaky Bucket Is Used For.
From www.greatideasforteachingmarketing.com
Leaky Bucket Theory Great Ideas for Teaching Marketing Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket is. Leaky Bucket Is Used For.
From www.istockphoto.com
Leaky Bucket Stock Illustration Download Image Now Bucket, Water Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the. Leaky Bucket Is Used For.
From slidemodel.com
Template of Leaky Bucket Strategy SlideModel Leaky Bucket Is Used For the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. Step 1 − let us. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the. Leaky Bucket Is Used For.
From www.gettyimages.com
317 Leaky Bucket Stock Photos, HighRes Pictures, and Images Getty Images Leaky Bucket Is Used For the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket. Leaky Bucket Is Used For.
From www.scaler.com
Leaky Bucket Algorithm Scalar Topics Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. Step 1 − let us. leaky bucket algorithm mainly controls the total amount and the rate of the traffic. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket stock image. Image of waste, running, holes 5839431 Leaky Bucket Is Used For Step 1 − let us. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket algorithm is a method of congestion control where multiple packets are stored. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket with Water on Background Stock Image Image of helpless Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the. Leaky Bucket Is Used For.
From www.researchgate.net
"leaky bucket" diagram used for AbCd evaluation in Zato shodera, snnp Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. Step 1. Leaky Bucket Is Used For.
From www.engati.com
Leaky Bucket Theory Engati Leaky Bucket Is Used For Step 1 − let us. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket algorithm is a method of congestion control where multiple packets are stored. Leaky Bucket Is Used For.
From www.researchgate.net
The leaky bucket states (A) overflown, and (B) nonoverflown Leaky Bucket Is Used For The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. . Leaky Bucket Is Used For.
From www.slideserve.com
PPT Token Bucket Leaky Bucket PowerPoint Presentation, free download Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. leaky bucket algorithm. Leaky Bucket Is Used For.
From www.alamy.com
Leaky Bucket Stock Photo Alamy Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. Step 1 − let us. the leaky bucket algorithm is a method of congestion control where multiple packets are. Leaky Bucket Is Used For.
From www.youtube.com
Leaky bucket and Token bucket with GATE PYQs. Clear Explanation YouTube Leaky Bucket Is Used For the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. the leaky bucket algorithm is a method of congestion control where multiple packets are stored temporarily. the use. Leaky Bucket Is Used For.
From usewhale.io
The Leaky Bucket Syndrome and how to combat knowledge loss Whale Leaky Bucket Is Used For Step 1 − let us. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. the use of the leaky bucket shapes the input traffic to make it conform to this commitment. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and. Leaky Bucket Is Used For.
From www.dreamstime.com
Leaky Bucket stock image. Image of leak, waste, bucket 5839431 Leaky Bucket Is Used For the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the leaky bucket is a traffic shaping and policing mechanism used in networking to control the flow of data packets. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in.. Leaky Bucket Is Used For.
From www.alamy.com
Leaky bucket with water isolated on white Stock Photo Alamy Leaky Bucket Is Used For leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in. the leaky bucket is used to implement traffic policing and traffic shaping in ethernet and cellular data networks. the. Leaky Bucket Is Used For.