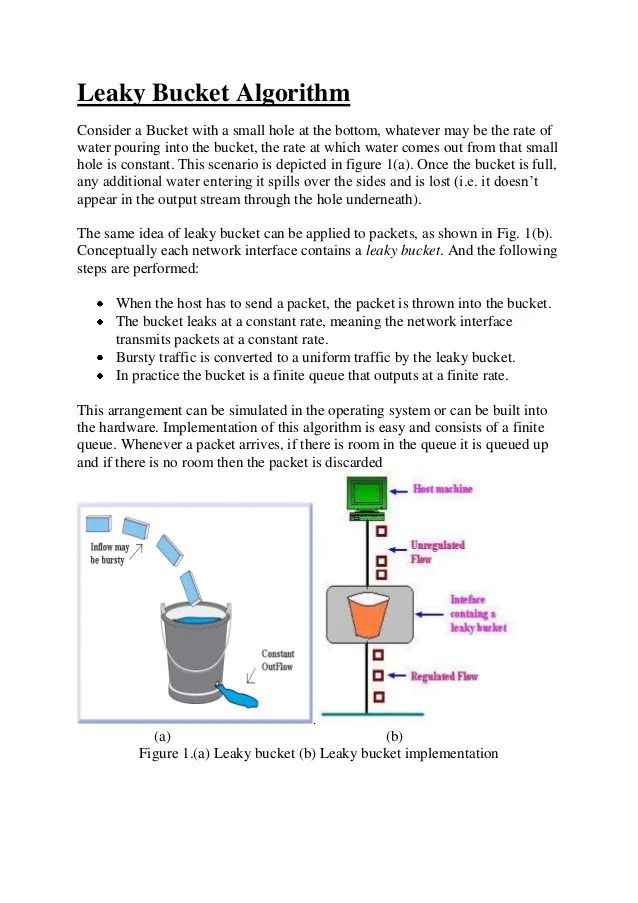
Leaky Bucket Algorithm Approach . It ensures that the flow of packets entering. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. Come down the rabbit hole with me to explore core concepts and master the fundamentals. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. By allowing a constant flow of. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. If you’re studying for gate or. Step 1 − let us imagine a. Discover the ins and outs of the leaky bucket algorithm for rate limiting. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion.
from www.slideshare.net
Discover the ins and outs of the leaky bucket algorithm for rate limiting. It ensures that the flow of packets entering. If you’re studying for gate or. Come down the rabbit hole with me to explore core concepts and master the fundamentals. Step 1 − let us imagine a. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. By allowing a constant flow of.
Leaky bucket algorithm
Leaky Bucket Algorithm Approach If you’re studying for gate or. Step 1 − let us imagine a. Come down the rabbit hole with me to explore core concepts and master the fundamentals. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. If you’re studying for gate or. By allowing a constant flow of. It ensures that the flow of packets entering. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Discover the ins and outs of the leaky bucket algorithm for rate limiting.
From www.researchgate.net
Leaky bucket algorithm Download Scientific Diagram Leaky Bucket Algorithm Approach Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. By allowing a constant flow of. It ensures that the. Leaky Bucket Algorithm Approach.
From www.scaler.com
Leaky Bucket Algorithm Scalar Topics Leaky Bucket Algorithm Approach The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. If you’re studying for gate or. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a simple yet effective way to control data flow and. Leaky Bucket Algorithm Approach.
From itnext.io
Rate limiting with leaky bucket algorithm by Codejitsu ITNEXT Leaky Bucket Algorithm Approach The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. It ensures that the flow of packets entering. Discover the ins and outs of the leaky bucket algorithm for rate limiting. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. Come down the rabbit. Leaky Bucket Algorithm Approach.
From www.youtube.com
leaky bucket algorithm congestion control networking Bhanu Priya YouTube Leaky Bucket Algorithm Approach Step 1 − let us imagine a. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. If you’re studying for gate or. It ensures that the flow of packets entering. Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm is a. Leaky Bucket Algorithm Approach.
From www.slideshare.net
Leaky bucket algorithm Leaky Bucket Algorithm Approach The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. Discover the ins and. Leaky Bucket Algorithm Approach.
From www.youtube.com
12. Leaky Bucket Algorithm Program VTU 5th Sem Computer Network Lab 15CSL57 YouTube Leaky Bucket Algorithm Approach The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. If you’re. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Chapter 13 PowerPoint Presentation, free download ID4138688 Leaky Bucket Algorithm Approach Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Discover the ins and outs of the leaky bucket algorithm for. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT The Network Layer PowerPoint Presentation, free download ID5856654 Leaky Bucket Algorithm Approach If you’re studying for gate or. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. It ensures that the flow of packets entering. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. The leaky bucket algorithm is a traffic shaping and policing technique used. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Bandwidth Management PowerPoint Presentation, free download ID4841716 Leaky Bucket Algorithm Approach Step 1 − let us imagine a. Discover the ins and outs of the leaky bucket algorithm for rate limiting. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. By allowing a constant flow of. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of. Leaky Bucket Algorithm Approach.
From it.wikipedia.org
Leaky bucket Wikipedia Leaky Bucket Algorithm Approach Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. By allowing a constant flow of. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks.. Leaky Bucket Algorithm Approach.
From www.studypool.com
SOLUTION Leaky Bucket Algorithm C Program Studypool Leaky Bucket Algorithm Approach By allowing a constant flow of. Come down the rabbit hole with me to explore core concepts and master the fundamentals. Step 1 − let us imagine a. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a traffic shaping and policing technique used to control the. Leaky Bucket Algorithm Approach.
From www.rdiachenko.com
Exploring and Implementing the Leaky Bucket Rate Limiting Algorithm Leaky Bucket Algorithm Approach Step 1 − let us imagine a. It ensures that the flow of packets entering. Discover the ins and outs of the leaky bucket algorithm for rate limiting. If you’re studying for gate or. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. By allowing a constant flow of. Leaky bucket. Leaky Bucket Algorithm Approach.
From www.researchgate.net
Intelligent leaky bucket algorithm. Download Scientific Diagram Leaky Bucket Algorithm Approach The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. If you’re studying for gate or. By allowing a constant flow of. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. It ensures that the flow of packets entering. Step 1 − let us. Leaky Bucket Algorithm Approach.
From www.youtube.com
Token and Leaky Bucket Algorithm YouTube Leaky Bucket Algorithm Approach A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Discover the ins and outs of the leaky bucket algorithm for rate limiting. Step 1 − let us imagine a.. Leaky Bucket Algorithm Approach.
From www.thetechnicaltalk.com
Differentiate between leaky bucket and token bucket methods of traffic shaping The Technical Talk Leaky Bucket Algorithm Approach A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Discover the ins and outs of the leaky bucket algorithm for rate limiting. If you’re studying for gate or. Leaky. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Principles of Congestion Control PowerPoint Presentation, free download ID8677065 Leaky Bucket Algorithm Approach If you’re studying for gate or. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. Step 1 − let us imagine a. It ensures that the flow of packets entering. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. By allowing a constant. Leaky Bucket Algorithm Approach.
From in.pinterest.com
Leaky Bucket Algorithm educlick Algorithm, Computer network, Networking Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. By allowing a constant flow of. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Step. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Chapter 18 Frame Relay PowerPoint Presentation, free download ID4121487 Leaky Bucket Algorithm Approach The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. If you’re studying for. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Chapter 13 PowerPoint Presentation, free download ID569119 Leaky Bucket Algorithm Approach By allowing a constant flow of. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. If you’re studying for gate or. It ensures that the flow of packets entering. Discover the ins and outs of. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Quality of Service Support PowerPoint Presentation, free download ID6577623 Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. If you’re studying for gate or. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. By allowing a constant flow of. The leaky bucket algorithm is a simple yet effective way to control data. Leaky Bucket Algorithm Approach.
From www.researchgate.net
Leaky bucket approach. Download Scientific Diagram Leaky Bucket Algorithm Approach A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. By allowing a constant flow of. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Step 1 − let us imagine a. If you’re studying for gate or. It ensures that the flow of. Leaky Bucket Algorithm Approach.
From www.youtube.com
Leaky Bucket vs Token Bucket Algorithm Leaky Bucket and Token Bucket Difference YouTube Leaky Bucket Algorithm Approach The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. A leaky bucket algorithm is a. Leaky Bucket Algorithm Approach.
From botpenguin.com
What is Leaky Bucket Theory & its Applications? Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. If you’re studying for gate or. Step 1 − let us imagine a. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are. Leaky Bucket Algorithm Approach.
From www.semanticscholar.org
[PDF] Leaky Bucket Algorithm for Congestion Control Semantic Scholar Leaky Bucket Algorithm Approach A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. If you’re studying for gate or. By allowing a constant flow of. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. The leaky bucket algorithm is a traffic shaping and policing technique used to. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT The Network Layer PowerPoint Presentation ID3653615 Leaky Bucket Algorithm Approach It ensures that the flow of packets entering. Step 1 − let us imagine a. By allowing a constant flow of. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. Come down the rabbit hole with me to explore core concepts and master the fundamentals. A leaky bucket algorithm is a. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Flow Control PowerPoint Presentation, free download ID418287 Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. By allowing a constant flow of. It ensures that the flow of packets entering. A leaky bucket algorithm is a method used in computer networks. Leaky Bucket Algorithm Approach.
From www.youtube.com
congestion control algorithm Leaky Bucket Algorithm (open loop and closed loop) YouTube Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. Step 1 − let us imagine a. Come down the rabbit hole with me to explore core concepts and master the fundamentals. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. Leaky bucket algorithm mainly controls the total. Leaky Bucket Algorithm Approach.
From www.tech-maze.info
System Design Leaky Bucket Algorithm And Its UsesSystem Design Rohit Modi Leaky Bucket Algorithm Approach The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Step 1 − let us imagine a. A leaky bucket algorithm is a method used in computer networks to control the. Leaky Bucket Algorithm Approach.
From www.youtube.com
Leaky Bucket Algorithm YouTube Leaky Bucket Algorithm Approach The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Step 1 − let us imagine a. It ensures that the flow of packets entering. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. If you’re studying for gate. Leaky Bucket Algorithm Approach.
From www.researchgate.net
Flowchart of the conventional leaky bucket algorithm. Download Scientific Diagram Leaky Bucket Algorithm Approach It ensures that the flow of packets entering. Leaky bucket algorithm mainly controls the total amount and the rate of the traffic sent to the network. The leaky bucket algorithm is a simple yet effective way to control data flow and prevent congestion. Discover the ins and outs of the leaky bucket algorithm for rate limiting. Step 1 − let. Leaky Bucket Algorithm Approach.
From www.youtube.com
Leaky bucket and Token bucket with GATE PYQs. Clear Explanation YouTube Leaky Bucket Algorithm Approach By allowing a constant flow of. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Step 1 − let us imagine a. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. If you’re studying for gate or. Come down. Leaky Bucket Algorithm Approach.
From eureka.patsnap.com
Leakybucketalgorithmbased energy consumption monitoring and analyzing method and system Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. Step 1 − let us imagine a. If you’re studying for gate or. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Come down the rabbit hole with me to explore core concepts and. Leaky Bucket Algorithm Approach.
From botpenguin.com
What is Leaky Bucket Theory & its Applications? Leaky Bucket Algorithm Approach Discover the ins and outs of the leaky bucket algorithm for rate limiting. Come down the rabbit hole with me to explore core concepts and master the fundamentals. By allowing a constant flow of. It ensures that the flow of packets entering. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Step. Leaky Bucket Algorithm Approach.
From songhayoung.github.io
[System Design] Leaky bucket / token bucket SUMFIのBlog Leaky Bucket Algorithm Approach Come down the rabbit hole with me to explore core concepts and master the fundamentals. The leaky bucket algorithm manages network traffic by controlling the rate at which data packets are transmitted. Step 1 − let us imagine a. By allowing a constant flow of. The leaky bucket algorithm is a simple yet effective way to control data flow and. Leaky Bucket Algorithm Approach.
From www.slideserve.com
PPT Outline PowerPoint Presentation, free download ID6256891 Leaky Bucket Algorithm Approach Come down the rabbit hole with me to explore core concepts and master the fundamentals. A leaky bucket algorithm is a method used in computer networks to control the rate of incoming traffic. The leaky bucket algorithm is a traffic shaping and policing technique used to control the rate of data transmission in computer networks. Leaky bucket algorithm mainly controls. Leaky Bucket Algorithm Approach.