Project overview: opensc
High level conclusions
Reachability and coverage overview
Warning:
The number of runtime covered functions are larger than the
number of reachable functions. This means that Fuzz Introspector found
there are more functions covered at runtime than what is considered
reachable based on the static analysis. This is a limitation in the
analysis as anything covered at runtime is by definition reachable by the
fuzzers.
This is likely due to a limitation in the static analysis. In this case, the
count of functions covered at runtime is the true value, which means this
is what should be considered "achieved" by the fuzzer.
Use the project functions table below to query all functions that were not covered at runtime.
Project functions overview
The following table shows data about each function in the project. The functions included in this table correspond to all functions that exist in the executables of the fuzzers. As such, there may be functions that are from third-party libraries.
For further technical details on the meaning of columns in the below table, please see the Glossary .
| Func name | Functions filename | Args | Function call depth | Reached by Fuzzers | Runtime reached by Fuzzers | Combined reached by Fuzzers | Fuzzers runtime hit | Func lines hit % | I Count | BB Count | Cyclomatic complexity | Functions reached | Reached by functions | Accumulated cyclomatic complexity | Undiscovered complexity |
|---|
Fuzzer details
Fuzzer: fuzz_asn1_print
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 3 | 2.70% |
| gold | [1:9] | 0 | 0.0% |
| yellow | [10:29] | 0 | 0.0% |
| greenyellow | [30:49] | 0 | 0.0% |
| lawngreen | 50+ | 108 | 97.2% |
| All colors | 111 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 1 | 0 | EP | call site: 00000 | fclose |
| 1 | 13 | print_tags_recursive | call site: 00013 | printf |
| 1 | 23 | sc_hex_dump | call site: 00023 | strlen |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_asn1_print.c | 1 |
| src/libopensc/asn1.c | 19 |
| src/libopensc/log.c | 3 |
| src/common/compat_strlcat.c | 1 |
| src/libopensc/sc.c | 1 |
Fuzzer: fuzz_pkcs11_uri
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 2 | 4.76% |
| gold | [1:9] | 8 | 19.0% |
| yellow | [10:29] | 7 | 16.6% |
| greenyellow | [30:49] | 1 | 2.38% |
| lawngreen | 50+ | 24 | 57.1% |
| All colors | 42 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 1 | 6 | parse_pkcs11_uri | call site: 00006 | fprintf |
| 1 | 20 | parse_pkcs11_uri | call site: 00020 | fprintf |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs11_uri.c | 1 |
| src/tests/fuzzing/../../tools/pkcs11_uri.c | 6 |
Fuzzer: fuzz_scconf_parse_string
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 4 | 4.93% |
| gold | [1:9] | 1 | 1.23% |
| yellow | [10:29] | 4 | 4.93% |
| greenyellow | [30:49] | 1 | 1.23% |
| lawngreen | 50+ | 71 | 87.6% |
| All colors | 81 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 1 | 6 | scconf_parse_string | call site: 00006 | buf_init |
| 1 | 9 | scconf_lex_engine | call site: 00009 | fgetc |
| 1 | 53 | scconf_parse_token | call site: 00053 | snprintf |
| 1 | 71 | scconf_lex_engine | call site: 00071 | snprintf |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_scconf_parse_string.c | 1 |
| src/scconf/scconf.c | 6 |
| src/scconf/parse.c | 11 |
| src/scconf/sclex.c | 8 |
| src/common/compat_strlcpy.c | 1 |
Fuzzer: fuzz_asn1_sig_value
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 355 | 65.2% |
| gold | [1:9] | 102 | 18.7% |
| yellow | [10:29] | 3 | 0.55% |
| greenyellow | [30:49] | 5 | 0.91% |
| lawngreen | 50+ | 79 | 14.5% |
| All colors | 544 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 77 | 342 | asn1_decode_entry | call site: 00342 | asn1_decode_path |
| 71 | 447 | asn1_encode | call site: 00447 | asn1_encode_path |
| 59 | 8 | sc_do_log | call site: 00008 | sc_do_log |
| 24 | 238 | load_card_drivers | call site: 00238 | load_dynamic_driver |
| 15 | 266 | load_card_atrs | call site: 00266 | scconf_get_str |
| 12 | 520 | asn1_encode_entry | call site: 00520 | asn1_write_element |
| 8 | 195 | scconf_get_str | call site: 00195 | sc_ctx_log_to_file |
| 7 | 334 | asn1_decode | call site: 00334 | sc_do_log |
| 6 | 146 | scconf_parse_token | call site: 00146 | scconf_parse_token |
| 6 | 325 | asn1_decode_entry | call site: 00325 | sc_do_log_color |
| 5 | 136 | scconf_parse_token | call site: 00136 | scconf_parse_reset_state |
| 5 | 155 | scconf_lex_engine | call site: 00155 | scconf_parse_token |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_asn1_sig_value.c | 1 |
| src/libopensc/ctx.c | 21 |
| src/libopensc/log.c | 8 |
| src/common/simclist.c | 12 |
| src/libopensc/card.c | 2 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 9 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/libopensc/asn1.c | 31 |
| src/libopensc/errors.c | 1 |
| src/libopensc/pkcs15-algo.c | 3 |
Fuzzer: fuzz_pkcs15_tool
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 2199 | 87.8% |
| gold | [1:9] | 4 | 0.15% |
| yellow | [10:29] | 55 | 2.19% |
| greenyellow | [30:49] | 14 | 0.55% |
| lawngreen | 50+ | 232 | 9.26% |
| All colors | 2504 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 1353 | 978 | sc_print_path | call site: 00978 | dump |
| 147 | 361 | sc_connect_card | call site: 00361 | sc_detect_escape_cmds |
| 127 | 850 | sc_unlock | call site: 00850 | parse_dir_record |
| 111 | 671 | sc_lock | call site: 00671 | sc_pkcs15_bind_internal |
| 76 | 544 | sc_connect_card | call site: 00544 | sc_card_sm_check |
| 70 | 2412 | sc_transmit_apdu | call site: 02412 | test_session_pin |
| 35 | 808 | sc_select_file | call site: 00808 | sc_read_binary |
| 33 | 630 | sc_connect_card | call site: 00630 | sc_pkcs15_bind |
| 24 | 270 | load_card_drivers | call site: 00270 | load_dynamic_driver |
| 17 | 2346 | sc_single_transmit | call site: 02346 | sc_sm_single_transmit |
| 15 | 298 | load_card_atrs | call site: 00298 | scconf_get_str |
| 14 | 46 | is_a_tty | call site: 00046 | isatty |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15_tool.c | 3 |
| src/tests/fuzzing/fuzzer_tool.c | 4 |
| src/tests/fuzzing/../../../src/tools/pkcs15-tool.c | 39 |
| src/tests/fuzzing/../../tools/util.c | 4 |
| src/libopensc/ctx.c | 23 |
| src/libopensc/log.c | 10 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 24 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 25 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/libopensc/errors.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 33 |
| src/libopensc/pkcs15-algo.c | 4 |
| src/libopensc/dir.c | 3 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/pkcs15.c | 53 |
| src/libopensc/pkcs15-prkey.c | 1 |
| src/libopensc/aux-data.c | 2 |
| src/libopensc/pkcs15-pubkey.c | 17 |
| src/libopensc/pkcs15-cert.c | 4 |
| src/libopensc/pkcs15-skey.c | 1 |
| src/libopensc/pkcs15-data.c | 3 |
| src/libopensc/pkcs15-pin.c | 10 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
| src/libopensc/pkcs15-cache.c | 3 |
| src/tools/../pkcs11/pkcs11-display.c | 2 |
| src/libopensc/compression.c | 4 |
| src/ui/notify.c | 1 |
| src/libopensc/sec.c | 1 |
| src/libopensc/base64.c | 2 |
| src/common/compat_strlcat.c | 1 |
| src/libopensc/apdu.c | 7 |
| src/libopensc/sm.c | 4 |
Fuzzer: fuzz_piv_tool
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 463 | 46.3% |
| gold | [1:9] | 45 | 4.50% |
| yellow | [10:29] | 32 | 3.20% |
| greenyellow | [30:49] | 40 | 4.00% |
| lawngreen | 50+ | 418 | 41.8% |
| All colors | 998 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 86 | 420 | asn1_decode_entry | call site: 00420 | asn1_decode_path |
| 62 | 553 | sc_card_sm_check | call site: 00553 | sc_card_sm_load |
| 24 | 277 | load_card_drivers | call site: 00277 | load_dynamic_driver |
| 20 | 843 | gen_key | call site: 00843 | sc_do_log_openssl |
| 18 | 359 | sc_connect_card | call site: 00359 | sc_detect_escape_cmds |
| 17 | 681 | sc_single_transmit | call site: 00681 | sc_sm_single_transmit |
| 15 | 305 | load_card_atrs | call site: 00305 | scconf_get_str |
| 14 | 53 | is_a_tty | call site: 00053 | isatty |
| 9 | 763 | sc_unlock | call site: 00763 | sc_do_log |
| 8 | 234 | scconf_get_str | call site: 00234 | sc_ctx_log_to_file |
| 8 | 534 | sc_connect_card | call site: 00534 | sc_do_log |
| 7 | 402 | asn1_decode_entry | call site: 00402 | asn1_decode |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_piv_tool.c | 5 |
| src/tests/fuzzing/fuzzer_tool.c | 7 |
| src/tests/fuzzing/../../../src/tools/piv-tool.c | 7 |
| src/tests/fuzzing/../../tools/util.c | 2 |
| src/libopensc/ctx.c | 22 |
| src/libopensc/log.c | 11 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 21 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 13 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/libopensc/errors.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 18 |
| src/libopensc/pkcs15-algo.c | 2 |
| src/libopensc/dir.c | 1 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/apdu.c | 8 |
| src/libopensc/sm.c | 4 |
| src/common/compat_strlcat.c | 1 |
Fuzzer: fuzz_card
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 357 | 50.4% |
| gold | [1:9] | 1 | 0.14% |
| yellow | [10:29] | 4 | 0.56% |
| greenyellow | [30:49] | 2 | 0.28% |
| lawngreen | 50+ | 343 | 48.5% |
| All colors | 707 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 507 | sc_card_sm_check | call site: 00507 | sc_card_sm_load |
| 39 | 382 | sc_asn1_decode_object_id | call site: 00382 | asn1_decode_path |
| 37 | 423 | sc_dump_oid | call site: 00423 | asn1_decode_se_info |
| 34 | 9 | sc_do_log | call site: 00009 | sc_color_fprintf |
| 24 | 239 | load_card_drivers | call site: 00239 | load_dynamic_driver |
| 18 | 313 | sc_connect_card | call site: 00313 | sc_detect_escape_cmds |
| 15 | 267 | load_card_atrs | call site: 00267 | scconf_get_str |
| 8 | 196 | scconf_get_str | call site: 00196 | sc_ctx_log_to_file |
| 7 | 356 | asn1_decode_entry | call site: 00356 | asn1_decode |
| 7 | 366 | asn1_decode | call site: 00366 | sc_do_log |
| 6 | 147 | scconf_parse_token | call site: 00147 | scconf_parse_token |
| 5 | 52 | list_delete_at | call site: 00052 | sc_do_log |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_card.c | 1 |
| src/libopensc/ctx.c | 22 |
| src/libopensc/log.c | 10 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 22 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 11 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 4 |
| src/libopensc/errors.c | 1 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 17 |
| src/libopensc/pkcs15-algo.c | 2 |
| src/libopensc/dir.c | 1 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/sec.c | 2 |
| src/common/compat_strlcat.c | 1 |
Fuzzer: fuzz_pkcs15_decode
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 387 | 31.5% |
| gold | [1:9] | 55 | 4.47% |
| yellow | [10:29] | 34 | 2.76% |
| greenyellow | [30:49] | 9 | 0.73% |
| lawngreen | 50+ | 743 | 60.5% |
| All colors | 1228 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 507 | sc_card_sm_check | call site: 00507 | sc_card_sm_load |
| 48 | 665 | sc_pkcs15_bind_synthetic | call site: 00665 | parse_emu_block |
| 34 | 9 | sc_do_log | call site: 00009 | sc_color_fprintf |
| 24 | 239 | load_card_drivers | call site: 00239 | load_dynamic_driver |
| 18 | 313 | sc_connect_card | call site: 00313 | sc_detect_escape_cmds |
| 15 | 267 | load_card_atrs | call site: 00267 | scconf_get_str |
| 9 | 965 | generate_cache_filename | call site: 00965 | sc_asn1_decode |
| 8 | 196 | scconf_get_str | call site: 00196 | sc_ctx_log_to_file |
| 7 | 453 | asn1_decode_entry | call site: 00453 | sc_do_log_color |
| 7 | 831 | parse_dir_record | call site: 00831 | sc_do_log |
| 7 | 919 | fix_authentic_ddo | call site: 00919 | sc_do_log_color |
| 6 | 147 | scconf_parse_token | call site: 00147 | scconf_parse_token |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15_decode.c | 2 |
| src/libopensc/ctx.c | 24 |
| src/libopensc/log.c | 8 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 22 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 22 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/errors.c | 1 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 18 |
| src/libopensc/pkcs15-algo.c | 3 |
| src/libopensc/dir.c | 3 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/pkcs15.c | 27 |
| src/libopensc/pkcs15-prkey.c | 1 |
| src/libopensc/aux-data.c | 1 |
| src/libopensc/pkcs15-pubkey.c | 8 |
| src/libopensc/pkcs15-cert.c | 1 |
| src/libopensc/pkcs15-skey.c | 1 |
| src/libopensc/pkcs15-data.c | 1 |
| src/libopensc/pkcs15-pin.c | 1 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
| src/libopensc/pkcs15-cache.c | 3 |
Fuzzer: fuzz_pkcs15_encode
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 587 | 35.3% |
| gold | [1:9] | 42 | 2.53% |
| yellow | [10:29] | 43 | 2.59% |
| greenyellow | [30:49] | 7 | 0.42% |
| lawngreen | 50+ | 981 | 59.0% |
| All colors | 1660 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 506 | sc_card_sm_check | call site: 00506 | sc_card_sm_load |
| 48 | 664 | sc_pkcs15_bind_synthetic | call site: 00664 | parse_emu_block |
| 34 | 8 | sc_do_log | call site: 00008 | sc_color_fprintf |
| 34 | 1333 | sc_pkcs15_decode_pubkey_rsa | call site: 01333 | sc_pkcs15_decode_pubkey_ec |
| 34 | 1476 | sc_pkcs15_encode_dodf_entry | call site: 01476 | sc_pkcs15_encode_skdf_entry |
| 24 | 238 | load_card_drivers | call site: 00238 | load_dynamic_driver |
| 24 | 1612 | sc_pkcs15_prkey_attrs_from_cert | call site: 01612 | sc_do_log_openssl |
| 18 | 312 | sc_connect_card | call site: 00312 | sc_detect_escape_cmds |
| 15 | 266 | load_card_atrs | call site: 00266 | scconf_get_str |
| 13 | 1368 | sc_pkcs15_decode_pubkey | call site: 01368 | sc_pkcs15_decode_pubkey |
| 11 | 1268 | sc_asn1_encode_algorithm_id | call site: 01268 | asn1_encode_se_info |
| 10 | 1282 | asn1_encode_entry | call site: 01282 | sc_do_log_color |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15_encode.c | 1 |
| src/libopensc/ctx.c | 24 |
| src/libopensc/log.c | 9 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 22 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 23 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/errors.c | 1 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 30 |
| src/libopensc/pkcs15-algo.c | 4 |
| src/libopensc/dir.c | 3 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/pkcs15.c | 43 |
| src/libopensc/pkcs15-prkey.c | 3 |
| src/libopensc/aux-data.c | 1 |
| src/libopensc/pkcs15-pubkey.c | 11 |
| src/libopensc/pkcs15-cert.c | 2 |
| src/libopensc/pkcs15-skey.c | 2 |
| src/libopensc/pkcs15-data.c | 2 |
| src/libopensc/pkcs15-pin.c | 2 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
| src/libopensc/pkcs15-cache.c | 3 |
| src/libopensc/compression.c | 4 |
Fuzzer: fuzz_pkcs15_crypt
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:
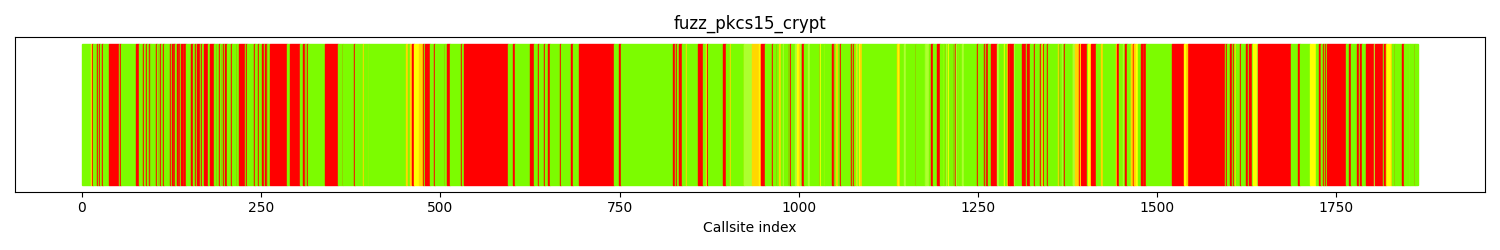
The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 637 | 34.1% |
| gold | [1:9] | 60 | 3.21% |
| yellow | [10:29] | 59 | 3.16% |
| greenyellow | [30:49] | 45 | 2.41% |
| lawngreen | 50+ | 1063 | 57.0% |
| All colors | 1864 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 532 | sc_card_sm_check | call site: 00532 | sc_card_sm_load |
| 49 | 1544 | sc_do_log_openssl | call site: 01544 | sc_do_log_openssl |
| 48 | 693 | sc_pkcs15_bind_synthetic | call site: 00693 | parse_emu_block |
| 47 | 1639 | sc_pkcs1_encode | call site: 01639 | sc_pkcs15_decipher |
| 26 | 1736 | asn1_encode_entry | call site: 01736 | asn1_encode_path |
| 24 | 261 | load_card_drivers | call site: 00261 | load_dynamic_driver |
| 18 | 338 | sc_connect_card | call site: 00338 | sc_detect_escape_cmds |
| 17 | 1519 | sc_pkcs1_strip_02_padding_constant_time | call site: 01519 | sc_pkcs1_strip_oaep_padding |
| 15 | 289 | load_card_atrs | call site: 00289 | scconf_get_str |
| 14 | 37 | is_a_tty | call site: 00037 | isatty |
| 11 | 1790 | sc_asn1_encode_algorithm_id | call site: 01790 | asn1_encode_se_info |
| 11 | 1803 | asn1_encode_entry | call site: 01803 | asn1_write_element |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15_crypt.c | 4 |
| src/tests/fuzzing/fuzzer_tool.c | 7 |
| src/tests/fuzzing/../../../src/tools/pkcs15-crypt.c | 8 |
| src/tests/fuzzing/../../tools/util.c | 2 |
| src/libopensc/ctx.c | 23 |
| src/libopensc/log.c | 9 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 28 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 27 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/libopensc/errors.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 31 |
| src/libopensc/pkcs15-algo.c | 4 |
| src/libopensc/dir.c | 3 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/pkcs15.c | 49 |
| src/libopensc/pkcs15-prkey.c | 1 |
| src/libopensc/aux-data.c | 1 |
| src/libopensc/pkcs15-pubkey.c | 3 |
| src/libopensc/pkcs15-cert.c | 1 |
| src/libopensc/pkcs15-skey.c | 1 |
| src/libopensc/pkcs15-data.c | 1 |
| src/libopensc/pkcs15-pin.c | 8 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
| src/libopensc/pkcs15-cache.c | 3 |
| src/libopensc/compression.c | 4 |
| src/ui/notify.c | 1 |
| src/libopensc/sec.c | 4 |
| src/libopensc/pkcs15-sec.c | 6 |
| src/libopensc/padding.c | 12 |
| src/libopensc/../../src/common/constant-time.h | 8 |
| src/libopensc/../../src/libopensc/sc-ossl-compat.h | 2 |
Fuzzer: fuzz_pkcs11
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 0 | 0.0% |
| gold | [1:9] | 0 | 0.0% |
| yellow | [10:29] | 0 | 0.0% |
| greenyellow | [30:49] | 0 | 0.0% |
| lawngreen | 50+ | 1 | 100.% |
| All colors | 1 | 100 |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs11.c | 1 |
Fuzzer: fuzz_pkcs15init
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 802 | 27.0% |
| gold | [1:9] | 133 | 4.47% |
| yellow | [10:29] | 162 | 5.45% |
| greenyellow | [30:49] | 69 | 2.32% |
| lawngreen | 50+ | 1804 | 60.7% |
| All colors | 2970 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 508 | sc_card_sm_check | call site: 00508 | sc_card_sm_load |
| 57 | 2517 | _pkcd15init_set_aux_md_data | call site: 02517 | sc_pkcs15_get_objects |
| 44 | 1857 | sc_pkcs15_bind_synthetic | call site: 01857 | parse_emu_block |
| 34 | 10 | sc_do_log | call site: 00010 | sc_color_fprintf |
| 26 | 783 | sc_profile_find_file_by_path | call site: 00783 | sc_profile_load |
| 24 | 240 | load_card_drivers | call site: 00240 | load_dynamic_driver |
| 23 | 2166 | sc_pkcs15init_store_pin | call site: 02166 | sc_pkcs15init_store_puk |
| 23 | 2629 | sc_pkcs15_free_certificate | call site: 02629 | sc_pkcs15_pubkey_from_prvkey |
| 18 | 314 | sc_connect_card | call site: 00314 | sc_detect_escape_cmds |
| 16 | 2679 | sc_pkcs15_encode_pubkey_ec | call site: 02679 | sc_pkcs15_encode_pubkey_eddsa |
| 15 | 268 | load_card_atrs | call site: 00268 | scconf_get_str |
| 15 | 1688 | sc_update_record | call site: 01688 | sc_lock |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15init.c | 11 |
| src/libopensc/ctx.c | 24 |
| src/libopensc/log.c | 8 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 28 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 34 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 3 |
| src/libopensc/errors.c | 1 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 33 |
| src/libopensc/pkcs15-algo.c | 4 |
| src/libopensc/dir.c | 8 |
| src/libopensc/ef-atr.c | 1 |
| src/tests/fuzzing/../../../src/pkcs15init/pkcs15-lib.c | 59 |
| src/tests/fuzzing/../../../src/pkcs15init/profile.c | 30 |
| src/libopensc/pkcs15.c | 59 |
| src/libopensc/pkcs15-prkey.c | 2 |
| src/libopensc/aux-data.c | 4 |
| src/libopensc/pkcs15-pubkey.c | 12 |
| src/libopensc/pkcs15-cert.c | 4 |
| src/libopensc/pkcs15-skey.c | 1 |
| src/libopensc/pkcs15-data.c | 1 |
| src/libopensc/pkcs15-pin.c | 8 |
| src/libopensc/pkcs15-cache.c | 3 |
| src/libopensc/compression.c | 4 |
| src/libopensc/sec.c | 1 |
| src/ui/notify.c | 1 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
Fuzzer: fuzz_pkcs15_reader
Call tree
The calltree shows the control flow of the fuzzer. This is overlaid with coverage information to display how much of the potential code a fuzzer can reach is in fact covered at runtime. In the following there is a link to a detailed calltree visualisation as well as a bitmap showing a high-level view of the calltree. For further information about these topics please see the glossary for full calltree and calltree overview
Call tree overview bitmap:

The distribution of callsites in terms of coloring is
| Color | Runtime hitcount | Callsite count | Percentage |
|---|---|---|---|
| red | 0 | 640 | 35.8% |
| gold | [1:9] | 24 | 1.34% |
| yellow | [10:29] | 43 | 2.40% |
| greenyellow | [30:49] | 29 | 1.62% |
| lawngreen | 50+ | 1050 | 58.7% |
| All colors | 1786 | 100 |
Fuzz blockers
The following nodes represent call sites where fuzz blockers occur.
| Amount of callsites blocked | Calltree index | Parent function | Callsite | Largest blocked function |
|---|---|---|---|---|
| 62 | 506 | sc_card_sm_check | call site: 00506 | sc_card_sm_load |
| 52 | 1469 | sc_do_log_openssl | call site: 01469 | sc_do_log_openssl |
| 48 | 664 | sc_pkcs15_bind_synthetic | call site: 00664 | parse_emu_block |
| 43 | 1647 | sc_pkcs1_encode | call site: 01647 | sc_pkcs15_decipher |
| 34 | 8 | sc_do_log | call site: 00008 | sc_color_fprintf |
| 24 | 238 | load_card_drivers | call site: 00238 | load_dynamic_driver |
| 23 | 1558 | sc_pkcs15_unwrap | call site: 01558 | use_key |
| 22 | 1592 | sc_pkcs15_wrap | call site: 01592 | use_key |
| 18 | 312 | sc_connect_card | call site: 00312 | sc_detect_escape_cmds |
| 17 | 1444 | sc_pkcs1_strip_02_padding_constant_time | call site: 01444 | sc_pkcs1_strip_oaep_padding |
| 15 | 266 | load_card_atrs | call site: 00266 | scconf_get_str |
| 10 | 1351 | _sc_pkcs15_verify_pin | call site: 01351 | sc_pkcs15_find_skey_by_id |
Runtime coverage analysis
| Function name | source code lines | source lines hit | percentage hit |
|---|
Files reached
| filename | functions hit |
|---|---|
| src/tests/fuzzing/fuzz_pkcs15_reader.c | 1 |
| src/libopensc/ctx.c | 24 |
| src/libopensc/log.c | 11 |
| src/common/simclist.c | 14 |
| src/libopensc/card.c | 28 |
| src/common/libscdl.c | 4 |
| src/libopensc/sc.c | 26 |
| src/scconf/scconf.c | 11 |
| src/scconf/parse.c | 12 |
| src/scconf/sclex.c | 9 |
| src/common/compat_strlcpy.c | 1 |
| src/libopensc/reader-ctapi.c | 1 |
| src/tests/fuzzing/fuzzer_reader.c | 4 |
| src/libopensc/errors.c | 1 |
| src/libopensc/reader-tr03119.c | 2 |
| src/libopensc/asn1.c | 18 |
| src/libopensc/pkcs15-algo.c | 3 |
| src/libopensc/dir.c | 3 |
| src/libopensc/ef-atr.c | 1 |
| src/libopensc/pkcs15.c | 43 |
| src/libopensc/pkcs15-prkey.c | 1 |
| src/libopensc/aux-data.c | 1 |
| src/libopensc/pkcs15-pubkey.c | 3 |
| src/libopensc/pkcs15-cert.c | 1 |
| src/libopensc/pkcs15-skey.c | 1 |
| src/libopensc/pkcs15-data.c | 1 |
| src/libopensc/pkcs15-pin.c | 10 |
| src/libopensc/pkcs15-syn.c | 3 |
| src/libopensc/pkcs15-emulator-filter.c | 3 |
| src/libopensc/pkcs15-cache.c | 3 |
| src/common/compat_strlcat.c | 1 |
| src/libopensc/pkcs15-sec.c | 10 |
| src/libopensc/padding.c | 12 |
| src/libopensc/sec.c | 6 |
| src/libopensc/compression.c | 4 |
| src/ui/notify.c | 1 |
| src/libopensc/../../src/common/constant-time.h | 8 |
| src/libopensc/../../src/libopensc/sc-ossl-compat.h | 2 |
Analyses and suggestions
Optimal target analysis
Remaining optimal interesting functions
The following table shows a list of functions that are optimal targets. Optimal targets are identified by finding the functions that in combination, yield a high code coverage.
| Func name | Functions filename | Arg count | Args | Function depth | hitcount | instr count | bb count | cyclomatic complexity | Reachable functions | Incoming references | total cyclomatic complexity | Unreached complexity |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
npa_init
|
/src/opensc/src/libopensc/card-npa.c | 1 | ['N/A'] | 18 | 0 | 153 | 21 | 10 | 474 | 0 | 3084 | 2087 |
iasecc_card_ctl
|
/src/opensc/src/libopensc/card-iasecc.c | 3 | ['N/A', 'size_t', 'N/A'] | 21 | 0 | 157 | 15 | 16 | 155 | 0 | 1576 | 685 |
pkcs15_create_object
|
/src/opensc/src/pkcs11/framework-pkcs15.c | 4 | ['N/A', 'N/A', 'size_t', 'N/A'] | 21 | 0 | 325 | 42 | 14 | 413 | 0 | 3429 | 495 |
cosm_emu_update_any_df
|
/src/opensc/src/pkcs15init/pkcs15-oberthur.c | 4 | ['N/A', 'N/A', 'int', 'N/A'] | 27 | 0 | 108 | 14 | 2 | 258 | 0 | 2163 | 450 |
pgp_card_ctl
|
/src/opensc/src/libopensc/card-openpgp.c | 3 | ['N/A', 'size_t', 'N/A'] | 19 | 0 | 284 | 42 | 7 | 145 | 0 | 1365 | 443 |
dnie_sm_get_wrapped_apdu
|
/src/opensc/src/libopensc/card-dnie.c | 3 | ['N/A', 'N/A', 'N/A'] | 18 | 0 | 183 | 32 | 10 | 134 | 0 | 1038 | 398 |
piv_init
|
/src/opensc/src/libopensc/card-piv.c | 1 | ['N/A'] | 20 | 0 | 454 | 65 | 20 | 137 | 0 | 1237 | 344 |
Implementing fuzzers that target the above functions will improve reachability such that it becomes:
All functions overview
If you implement fuzzers for these functions, the status of all functions in the project will be:
| Func name | Functions filename | Args | Function call depth | Reached by Fuzzers | Runtime reached by Fuzzers | Combined reached by Fuzzers | Fuzzers runtime hit | Func lines hit % | I Count | BB Count | Cyclomatic complexity | Functions reached | Reached by functions | Accumulated cyclomatic complexity | Undiscovered complexity |
|---|
Fuzz engine guidance
This sections provides heuristics that can be used as input to a fuzz engine when running a given fuzz target. The current focus is on providing input that is usable by libFuzzer.
src/tests/fuzzing/fuzz_asn1_print.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['print_tags_recursive', 'sc_hex_dump']src/tests/fuzzing/fuzz_pkcs11_uri.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['parse_pkcs11_uri']src/tests/fuzzing/fuzz_scconf_parse_string.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['scconf_parse_string', 'scconf_lex_engine', 'scconf_parse_token']src/tests/fuzzing/fuzz_asn1_sig_value.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['asn1_decode_entry', 'asn1_encode', 'sc_do_log', 'load_card_drivers', 'load_card_atrs', 'asn1_encode_entry', 'scconf_get_str', 'asn1_decode', 'scconf_parse_token']src/tests/fuzzing/fuzz_pkcs15_tool.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_print_path', 'sc_connect_card', 'sc_unlock', 'sc_lock', 'sc_transmit_apdu', 'sc_select_file', 'load_card_drivers', 'sc_single_transmit']src/tests/fuzzing/fuzz_piv_tool.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['asn1_decode_entry', 'sc_card_sm_check', 'load_card_drivers', 'gen_key', 'sc_connect_card', 'sc_single_transmit', 'load_card_atrs', 'is_a_tty', 'sc_unlock', 'scconf_get_str']src/tests/fuzzing/fuzz_card.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', 'sc_asn1_decode_object_id', 'sc_dump_oid', 'sc_do_log', 'load_card_drivers', 'sc_connect_card', 'load_card_atrs', 'scconf_get_str', 'asn1_decode_entry', 'asn1_decode']src/tests/fuzzing/fuzz_pkcs15_decode.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', 'sc_pkcs15_bind_synthetic', 'sc_do_log', 'load_card_drivers', 'sc_connect_card', 'load_card_atrs', 'generate_cache_filename', 'scconf_get_str', 'asn1_decode_entry', 'parse_dir_record']src/tests/fuzzing/fuzz_pkcs15_encode.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', 'sc_pkcs15_bind_synthetic', 'sc_do_log', 'sc_pkcs15_decode_pubkey_rsa', 'sc_pkcs15_encode_dodf_entry', 'load_card_drivers', 'sc_pkcs15_prkey_attrs_from_cert', 'sc_connect_card', 'load_card_atrs', 'sc_pkcs15_decode_pubkey']src/tests/fuzzing/fuzz_pkcs15_crypt.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', 'sc_do_log_openssl', 'sc_pkcs15_bind_synthetic', 'sc_pkcs1_encode', 'asn1_encode_entry', 'load_card_drivers', 'sc_connect_card', 'sc_pkcs1_strip_02_padding_constant_time', 'load_card_atrs', 'is_a_tty']src/tests/fuzzing/fuzz_pkcs11.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
src/tests/fuzzing/fuzz_pkcs15init.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', '_pkcd15init_set_aux_md_data', 'sc_pkcs15_bind_synthetic', 'sc_do_log', 'sc_profile_find_file_by_path', 'load_card_drivers', 'sc_pkcs15init_store_pin', 'sc_pkcs15_free_certificate', 'sc_connect_card', 'sc_pkcs15_encode_pubkey_ec']src/tests/fuzzing/fuzz_pkcs15_reader.c
Dictionary
Use this with the libFuzzer -dict=DICT.file flag
Fuzzer function priority
Use one of these functions as input to libfuzzer with flag: -focus_function name
-focus_function=['sc_card_sm_check', 'sc_do_log_openssl', 'sc_pkcs15_bind_synthetic', 'sc_pkcs1_encode', 'sc_do_log', 'load_card_drivers', 'sc_pkcs15_unwrap', 'sc_pkcs15_wrap', 'sc_connect_card', 'sc_pkcs1_strip_02_padding_constant_time']Runtime coverage analysis
This section shows analysis of runtime coverage data.
For futher technical details on how this section is generated, please see the Glossary .
Complex functions with low coverage
| Func name | Function total lines | Lines covered at runtime | percentage covered | Reached by fuzzers |
|---|---|---|---|---|
| load_card_atrs | 54 | 12 | 22.22% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_decode', 'fuzz_piv_tool', 'fuzz_pkcs15init', 'fuzz_card', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_tool'] |
| sc_color_fprintf_va | 52 | 9 | 17.30% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_decode', 'fuzz_piv_tool', 'fuzz_pkcs15init', 'fuzz_card', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_tool'] |
| piv_read_obj_from_file | 56 | 23 | 41.07% | ['fuzz_pkcs15_reader', 'fuzz_piv_tool'] |
| sc_card_sm_check | 51 | 9 | 17.64% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_piv_tool', 'fuzz_pkcs15init', 'fuzz_card', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_tool'] |
| pgp_get_pubkey_pem | 94 | 14 | 14.89% | ['fuzz_pkcs15init', 'fuzz_card'] |
| gnuk_write_certificate | 34 | 11 | 32.35% | ['fuzz_card'] |
| cwa_create_secure_channel | 292 | 30 | 10.27% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_card', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_apdu2bytes | 69 | 19 | 27.53% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| atrust_acos_select_aid | 31 | 17 | 54.83% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt'] |
| authentic_parse_credential_data | 59 | 32 | 54.23% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| dnie_pin_cmd | 40 | 21 | 52.5% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt'] |
| entersafe_pin_cmd | 36 | 12 | 33.33% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| epass2003_pin_cmd | 49 | 13 | 26.53% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| gids_read_binary | 35 | 9 | 25.71% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| gids_card_ctl | 34 | 13 | 38.23% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| gids_get_pin_status | 41 | 13 | 31.70% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| iasecc_card_ctl | 36 | 18 | 50.0% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| iasecc_pin_get_policy | 81 | 40 | 49.38% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_hsm_pin_cmd | 127 | 48 | 37.79% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| iasecc_sm_initialize | 44 | 15 | 34.09% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| iasecc_sm_se_mutual_authentication | 34 | 17 | 50.0% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_pkcs15emu_eoi_init_ex | 59 | 25 | 42.37% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_pkcs15emu_esteid2018_init | 173 | 49 | 28.32% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] |
| sc_pkcs15emu_gids_init | 104 | 11 | 10.57% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| itacns_check_and_add_keyset | 79 | 39 | 49.36% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt'] |
| itacns_add_cert | 54 | 23 | 42.59% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt'] |
| sc_pkcs15emu_sc_hsm_init | 207 | 52 | 25.12% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_pkcs15_bind_synthetic | 74 | 25 | 33.78% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs15init', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_tool'] |
| sc_pin_cmd | 57 | 31 | 54.38% | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_reader', 'fuzz_pkcs15_decode', 'fuzz_pkcs15init', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15_tool'] |
| sc_pkcs15_prkey_attrs_from_cert | 59 | 24 | 40.67% | ['fuzz_pkcs15_encode'] |
| myeid_set_security_env | 61 | 29 | 47.54% | ['fuzz_pkcs15_reader', 'fuzz_pkcs11', 'fuzz_pkcs15_crypt'] |
| pgp_decipher | 97 | 48 | 49.48% | ['fuzz_pkcs15_reader', 'fuzz_pkcs15_crypt'] |
| rutoken_card_ctl | 51 | 19 | 37.25% | ['fuzz_pkcs11', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init'] |
| sc_pkcs15_get_application_by_type | 34 | 14 | 41.17% | ['fuzz_pkcs11'] |
| _get_auth_object_by_name | 51 | 13 | 25.49% | ['fuzz_pkcs11'] |
| register_xeddsa_mechanisms | 39 | 18 | 46.15% | ['fuzz_pkcs11'] |
| pkcs15_init_pin | 67 | 32 | 47.76% | ['fuzz_pkcs11'] |
| pkcs15_gen_keypair | 191 | 42 | 21.98% | ['fuzz_pkcs11'] |
| pkcs15_cert_get_attribute | 89 | 27 | 30.33% | ['fuzz_pkcs11'] |
| pkcs15_cert_cmp_attribute | 51 | 16 | 31.37% | ['fuzz_pkcs11'] |
| pkcs15_prkey_get_attribute | 185 | 73 | 39.45% | ['fuzz_pkcs11'] |
| pkcs15_prkey_can_do | 39 | 14 | 35.89% | ['fuzz_pkcs11'] |
| pkcs15_prkey_init_params | 58 | 21 | 36.20% | ['fuzz_pkcs11'] |
| pkcs15_pubkey_get_attribute | 191 | 87 | 45.54% | ['fuzz_pkcs11'] |
| pkcs15_dobj_get_attribute | 77 | 20 | 25.97% | ['fuzz_pkcs11'] |
| pkcs15_skey_get_attribute | 99 | 35 | 35.35% | ['fuzz_pkcs11'] |
| pkcs15_skey_decrypt | 48 | 20 | 41.66% | ['fuzz_pkcs11'] |
| sc_pkcs11_register_mechanism | 41 | 19 | 46.34% | ['fuzz_pkcs11'] |
| sc_pkcs11_verify_init | 42 | 22 | 52.38% | ['fuzz_pkcs11'] |
| push_login_state | 33 | 6 | 18.18% | ['fuzz_pkcs11'] |
| load_pkcs11_parameters | 56 | 26 | 46.42% | ['fuzz_pkcs11'] |
| sc_pkcs11_verify_data | 329 | 158 | 48.02% | ['fuzz_pkcs11'] |
| sc_pkcs11_init_lock | 33 | 7 | 21.21% | ['fuzz_pkcs11'] |
| C_UnwrapKey | 52 | 28 | 53.84% | ['fuzz_pkcs11'] |
| C_DeriveKey | 59 | 30 | 50.84% | ['fuzz_pkcs11'] |
| card_detect | 137 | 15 | 10.94% | ['fuzz_pkcs11'] |
| card_detect_all | 35 | 7 | 20.0% | ['fuzz_pkcs11'] |
| sc_pkcs15init_bind | 93 | 50 | 53.76% | ['fuzz_pkcs11'] |
| sc_pkcs15init_store_certificate | 79 | 16 | 20.25% | ['fuzz_pkcs11'] |
| authentic_manage_sdo_encode | 65 | 33 | 50.76% | ['fuzz_pkcs15init'] |
| iasecc_create_file | 41 | 20 | 48.78% | ['fuzz_pkcs15init'] |
| iasecc_get_free_reference | 85 | 31 | 36.47% | ['fuzz_pkcs15init'] |
| iasecc_pin_verify | 65 | 28 | 43.07% | ['fuzz_pkcs15init'] |
| isoApplet_ctl_generate_key | 144 | 75 | 52.08% | ['fuzz_pkcs15init'] |
| muscle_pin_cmd | 71 | 27 | 38.02% | ['fuzz_pkcs15init'] |
| myeid_loadkey | 45 | 21 | 46.66% | ['fuzz_pkcs15init'] |
| auth_update_component | 85 | 25 | 29.41% | ['fuzz_pkcs15init'] |
| sc_update_record | 34 | 10 | 29.41% | ['fuzz_pkcs15init'] |
| iasecc_sdo_allocate_and_parse | 40 | 19 | 47.5% | ['fuzz_pkcs15init'] |
| authentic_pkcs15_fix_file_access_rule | 33 | 18 | 54.54% | ['fuzz_pkcs15init'] |
| authentic_pkcs15_generate_key | 44 | 17 | 38.63% | ['fuzz_pkcs15init'] |
| cardos_generate_key | 69 | 21 | 30.43% | ['fuzz_pkcs15init'] |
| cflex_create_dummy_chvs | 41 | 13 | 31.70% | ['fuzz_pkcs15init'] |
| cflex_create_key | 36 | 12 | 33.33% | ['fuzz_pkcs15init'] |
| entersafe_create_dir | 82 | 25 | 30.48% | ['fuzz_pkcs15init'] |
| entersafe_sanity_check | 37 | 16 | 43.24% | ['fuzz_pkcs15init'] |
| epass2003_pkcs15_init_card | 37 | 18 | 48.64% | ['fuzz_pkcs15init'] |
| epass2003_pkcs15_sanity_check | 44 | 17 | 38.63% | ['fuzz_pkcs15init'] |
| iasecc_pkcs15_erase_card | 60 | 11 | 18.33% | ['fuzz_pkcs15init'] |
| iasecc_pkcs15_create_key | 42 | 17 | 40.47% | ['fuzz_pkcs15init'] |
| iasecc_sdo_allocate_pubkey | 58 | 18 | 31.03% | ['fuzz_pkcs15init'] |
| isoApplet_generate_key_ec | 135 | 61 | 45.18% | ['fuzz_pkcs15init'] |
| sc_pkcs15init_generate_secret_key | 42 | 11 | 26.19% | ['fuzz_pkcs15init'] |
| openpgp_store_key | 50 | 15 | 30.0% | ['fuzz_pkcs15init'] |
| rtecp_create_pin | 73 | 19 | 26.02% | ['fuzz_pkcs15init'] |
| sc_hsm_emu_update_any_df | 43 | 16 | 37.20% | ['fuzz_pkcs15init'] |
| setcos_init_card | 35 | 18 | 51.42% | ['fuzz_pkcs15init'] |
| setcos_create_pin | 32 | 9 | 28.12% | ['fuzz_pkcs15init'] |
| starcos_write_pukey | 65 | 20 | 30.76% | ['fuzz_pkcs15init'] |
| starcos_generate_key | 45 | 19 | 42.22% | ['fuzz_pkcs15init'] |
| asepcos_pin_cmd | 88 | 9 | 10.22% | ['fuzz_pkcs15_reader'] |
| auth_pin_reset_oberthur_style | 82 | 13 | 15.85% | ['fuzz_pkcs15_reader'] |
| sc_pkcs15_unwrap | 61 | 32 | 52.45% | ['fuzz_pkcs15_reader'] |
| sc_pkcs15_wrap | 80 | 41 | 51.24% | ['fuzz_pkcs15_reader'] |
Files and Directories in report
This section shows which files and directories are considered in this report. The main reason for showing this is fuzz introspector may include more code in the reasoning than is desired. This section helps identify if too many files/directories are included, e.g. third party code, which may be irrelevant for the threat model. In the event too much is included, fuzz introspector supports a configuration file that can exclude data from the report. See the following link for more information on how to create a config file: link
Files in report
| Source file | Reached by | Covered by |
|---|---|---|
| [] | [] | |
| /src/opensc/src/libopensc/card-dtrust.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-dtrust.c | [] | [] |
| /src/opensc/src/libopensc/asn1.c | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-algo.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-cache.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-iasecc.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15_encode.c | ['fuzz_pkcs15_encode'] | ['fuzz_pkcs15_encode'] |
| /src/opensc/src/libopensc/log.c | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-iasecc.c | [] | [] |
| /src/opensc/openpace/src/eac.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-authentic.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-lib.c | [] | [] |
| /src/opensc/openpace/src/eac_kdf.c | [] | [] |
| /src/opensc/openpace/src/eac_dh.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-starcert.c | [] | [] |
| /src/opensc/src/libopensc/card-edo.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-coolkey.c | [] | [] |
| /src/opensc/src/libopensc/simpletlv.c | [] | [] |
| /src/opensc/src/libopensc/reader-tr03119.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | [] |
| /src/opensc/src/pkcs15init/pkcs15-entersafe.c | [] | [] |
| /src/opensc/src/libopensc/../../src/libopensc/sc-ossl-compat.h | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] | [] |
| /src/opensc/src/libopensc/pkcs15-din-66291.c | [] | [] |
| /src/opensc/src/libopensc/card-atrust-acos.c | [] | [] |
| /src/opensc/src/libopensc/sm.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool'] | ['fuzz_piv_tool'] |
| /src/opensc/src/libopensc/pkcs15-lteid.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-atrust-acos.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_asn1_print.c | ['fuzz_asn1_print'] | ['fuzz_asn1_print'] |
| /src/opensc/src/libopensc/pkcs15-esteid2018.c | [] | [] |
| /src/opensc/src/pkcs11/mechanism.c | [] | [] |
| /src/opensc/src/libopensc/sc.c | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_print', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-asepcos.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-skey.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15init'] |
| /src/opensc/src/pkcs11/misc.c | [] | [] |
| /src/opensc/src/libopensc/card-npa.c | [] | [] |
| /src/opensc/openpace/src/eac_ca.c | [] | [] |
| /usr/include/x86_64-linux-gnu/bits/uintn-identity.h | [] | [] |
| /src/opensc/src/scconf/scconf.c | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/reader-ctapi.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-nqApplet.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-eoi.c | [] | [] |
| /src/opensc/src/pkcs11/pkcs11-global.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-sc-hsm.c | [] | [] |
| /src/opensc/src/tools/../pkcs11/pkcs11-display.c | ['fuzz_pkcs15_tool'] | [] |
| /src/opensc/src/libopensc/iso7816.c | [] | [] |
| /src/opensc/src/libopensc/aux-data.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-oberthur-awp.c | [] | [] |
| /src/opensc/src/libopensc/gp.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzzer_reader.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-sec.c | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] |
| /src/opensc/openpace/src/x509_lookup.c | [] | [] |
| /src/opensc/openpace/src/ta.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_scconf_parse_string.c | ['fuzz_scconf_parse_string'] | ['fuzz_scconf_parse_string'] |
| /src/opensc/src/libopensc/card-lteid.c | [] | [] |
| /src/opensc/src/libopensc/card-esteid2025.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15_decode.c | ['fuzz_pkcs15_decode'] | ['fuzz_pkcs15_decode'] |
| /src/opensc/src/libopensc/card-dnie.c | [] | [] |
| /src/opensc/src/libopensc/card-coolkey.c | [] | [] |
| /src/opensc/src/sm/sm-iso.c | [] | [] |
| /src/opensc/src/common/compat_strlcat.c | ['fuzz_asn1_print', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_print', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_reader'] |
| /src/opensc/openpace/src/eac_util.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-esteid2025.c | [] | [] |
| /src/opensc/src/libopensc/./../tools/fread_to_eof.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../../src/tools/piv-tool.c | ['fuzz_piv_tool'] | [] |
| /src/opensc/src/libopensc/card-mcrd.c | [] | [] |
| /src/opensc/src/libopensc/card-belpic.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-cert.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/tests/fuzzing/fuzz_piv_tool.c | ['fuzz_piv_tool'] | ['fuzz_piv_tool'] |
| /src/opensc/src/libopensc/card-piv.c | [] | [] |
| /src/opensc/src/common/libscdl.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | [] |
| /src/opensc/src/libopensc/card-sc-hsm.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../../src/tools/pkcs15-crypt.c | ['fuzz_pkcs15_crypt'] | [] |
| /src/opensc/src/libopensc/card-idprime.c | [] | [] |
| /src/opensc/src/libopensc/card-cac-common.c | [] | [] |
| /src/opensc/src/libopensc/card-asepcos.c | [] | [] |
| /src/opensc/src/libopensc/ctx.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-muscle.c | [] | [] |
| /src/opensc/src/libopensc/ef-gdo.c | [] | [] |
| /src/opensc/src/libopensc/card-openpgp.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-data.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-idprime.c | [] | [] |
| /src/opensc/openpace/src/pace.c | [] | [] |
| /src/opensc/openpace/src/eac_ecdh.c | [] | [] |
| /src/opensc/src/libopensc/card-isoApplet.c | [] | [] |
| /src/opensc/src/libopensc/card-epass2003.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-esinit.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-syn.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs11/framework-pkcs15init.c | [] | [] |
| /src/opensc/src/libopensc/../../src/common/constant-time.h | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] | [] |
| /src/opensc/src/libopensc/card-esteid2018.c | [] | [] |
| /src/opensc/src/scconf/sclex.c | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/errors.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/openpace/src/cvc_lookup.c | [] | [] |
| /src/opensc/src/scconf/parse.c | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-myeid.c | [] | [] |
| /src/opensc/src/libopensc/card-rtecp.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-tcos.c | [] | [] |
| /src/opensc/src/libopensc/card-rutoken.c | [] | [] |
| /src/opensc/openpace/src/objects.c | [] | [] |
| /src/opensc/openpace/src/ri_lib.c | [] | [] |
| /src/opensc/src/libopensc/card-gemsafeV1.c | [] | [] |
| /src/opensc/src/pkcs11/../../src/common/constant-time.h | [] | [] |
| /src/opensc/src/pkcs11/openssl.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15_tool.c | ['fuzz_pkcs15_tool'] | ['fuzz_pkcs15_tool'] |
| /src/opensc/src/libopensc/compression.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-itacns.c | [] | [] |
| /src/opensc/src/libopensc/card-iasecc.c | [] | [] |
| /src/opensc/src/pkcs11/debug.c | [] | [] |
| /src/opensc/src/pkcs15init/profile.c | [] | [] |
| /src/opensc/src/sm/sm-eac.c | [] | [] |
| /src/opensc/src/libopensc/padding.c | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-myeid.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15_crypt.c | ['fuzz_pkcs15_crypt'] | ['fuzz_pkcs15_crypt'] |
| /src/opensc/src/libopensc/pkcs15-piv.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-cflex.c | [] | [] |
| /src/opensc/src/pkcs11/pkcs11-display.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-emulator-filter.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | [] |
| /src/opensc/openpace/src/eac_lib.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-gemsafeV1.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-prkey.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/pkcs15init/pkcs15-starcos.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15init.c | ['fuzz_pkcs15init'] | ['fuzz_pkcs15init'] |
| /src/opensc/src/libopensc/cwa-dnie.c | [] | [] |
| /src/opensc/openpace/src/pace_lib.c | [] | [] |
| /src/opensc/src/libopensc/cwa14890.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_asn1_sig_value.c | ['fuzz_asn1_sig_value'] | ['fuzz_asn1_sig_value'] |
| /src/opensc/src/libopensc/pkcs15-cac.c | [] | [] |
| /src/opensc/src/pkcs11/pkcs11-object.c | [] | [] |
| /src/opensc/openpace/src/eac_asn1.c | [] | [] |
| /src/opensc/src/libopensc/card-authentic.c | [] | [] |
| /src/opensc/src/pkcs11/framework-pkcs15.c | [] | [] |
| /src/opensc/src/libopensc/card-flex.c | [] | [] |
| /src/opensc/src/common/simclist.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-default.c | [] | [] |
| /src/opensc/src/libopensc/card-eoi.c | [] | [] |
| /src/opensc/src/libopensc/card-starcos.c | [] | [] |
| /src/opensc/openpace/src/pace_mappings.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-starcos-esign.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../../src/pkcs15init/profile.c | ['fuzz_pkcs15init'] | [] |
| /src/opensc/src/tests/fuzzing/../../../src/tools/pkcs15-tool.c | ['fuzz_pkcs15_tool'] | [] |
| /src/opensc/src/libopensc/pkcs15-pin.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-dnie.c | [] | [] |
| /src/opensc/openpace/src/ta_lib.c | [] | [] |
| /src/opensc/src/libopensc/base64.c | ['fuzz_pkcs15_tool'] | [] |
| /src/opensc/src/libopensc/card-setcos.c | [] | [] |
| /src/opensc/src/libopensc/ef-atr.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-oberthur.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../tools/util.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_pkcs15_crypt'] | [] |
| /src/opensc/src/pkcs15init/pkcs15-epass2003.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../../src/pkcs15init/pkcs15-lib.c | ['fuzz_pkcs15init'] | [] |
| /src/opensc/src/libopensc/pkcs15-openpgp.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-cardos.c | [] | [] |
| /src/opensc/src/pkcs11/pkcs11-session.c | [] | [] |
| /src/opensc/src/libopensc/card-itacns.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-pteid.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-jpki.c | [] | [] |
| /src/opensc/src/libopensc/card-muscle.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzzer_tool.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_pkcs15_crypt'] | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_pkcs15_crypt'] |
| /src/opensc/src/libopensc/iasecc-sm.c | [] | [] |
| /src/opensc/src/ui/notify.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-cac.c | [] | [] |
| /src/opensc/openpace/src/misc.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-skeid.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs15_reader.c | ['fuzz_pkcs15_reader'] | ['fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-skeid.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-setcos.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs11_uri.c | ['fuzz_pkcs11_uri'] | ['fuzz_pkcs11_uri'] |
| /src/opensc/src/libopensc/iasecc-sdo.c | [] | [] |
| /src/opensc/src/libopensc/apdu.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool'] | ['fuzz_pkcs15_tool', 'fuzz_piv_tool'] |
| /src/opensc/src/libopensc/sec.c | ['fuzz_pkcs15_tool', 'fuzz_card', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_card', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-masktech.c | [] | [] |
| /usr/include/openssl/x509.h | [] | [] |
| /src/opensc/src/libopensc/pkcs15-nqApplet.c | [] | [] |
| /src/opensc/src/libopensc/dir.c | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/card-cardos.c | [] | [] |
| /src/opensc/src/libopensc/card-cardos-common.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-rutoken.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-openpgp.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-gids.c | [] | [] |
| /src/opensc/src/tests/fuzzing/../../tools/pkcs11_uri.c | ['fuzz_pkcs11_uri'] | [] |
| /src/opensc/src/libopensc/card-jpki.c | [] | [] |
| /src/opensc/src/libopensc/card-gids.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-oberthur.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_card.c | ['fuzz_card'] | ['fuzz_card'] |
| /src/opensc/src/libopensc/card.c | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-cardos.c | [] | [] |
| /src/opensc/src/tests/fuzzing/fuzz_pkcs11.c | ['fuzz_pkcs11'] | ['fuzz_pkcs11'] |
| /src/opensc/src/pkcs15init/pkcs15-rtecp.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-sc-hsm.c | [] | [] |
| /src/opensc/src/libopensc/ctbcs.c | [] | [] |
| /src/opensc/openpace/src/ca_lib.c | [] | [] |
| /src/opensc/src/common/compat_strlcpy.c | ['fuzz_scconf_parse_string', 'fuzz_asn1_sig_value', 'fuzz_pkcs15_tool', 'fuzz_piv_tool', 'fuzz_card', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_scconf_parse_string', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/src/libopensc/pkcs15-tccardos.c | [] | [] |
| /src/opensc/src/pkcs11/slot.c | [] | [] |
| /src/opensc/openpace/src/cv_cert.c | [] | [] |
| /src/opensc/src/libopensc/card-tcos.c | [] | [] |
| /src/opensc/src/libopensc/pkcs15-pubkey.c | ['fuzz_pkcs15_tool', 'fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] | ['fuzz_pkcs15_decode', 'fuzz_pkcs15_encode', 'fuzz_pkcs15_crypt', 'fuzz_pkcs15init', 'fuzz_pkcs15_reader'] |
| /src/opensc/openpace/src/ssl_compat.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-isoApplet.c | [] | [] |
| /src/opensc/src/libopensc/card-cac1.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-oberthur.c | [] | [] |
| /src/opensc/src/libopensc/muscle.c | [] | [] |
| /src/opensc/src/libopensc/muscle-filesystem.c | [] | [] |
| /src/opensc/src/libopensc/card-entersafe.c | [] | [] |
| /src/opensc/src/pkcs15init/pkcs15-gids.c | [] | [] |
| /src/opensc/src/pkcs11/../../src/libopensc/sc-ossl-compat.h | [] | [] |
| /src/opensc/src/libopensc/pkcs15-actalis.c | [] | [] |
Directories in report
| Directory |
|---|
| /src/opensc/src/libopensc/./../tools/ |
| /usr/include/openssl/ |
| /src/opensc/src/ui/ |
| /src/opensc/src/pkcs15init/ |
| /src/opensc/src/scconf/ |
| /src/opensc/src/tests/fuzzing/ |
| /src/opensc/src/common/ |
| /src/opensc/src/libopensc/../../src/libopensc/ |
| /src/opensc/src/pkcs11/../../src/libopensc/ |
| /src/opensc/src/tests/fuzzing/../../../src/pkcs15init/ |
| /src/opensc/src/tools/../pkcs11/ |
| /src/opensc/src/pkcs11/ |
| /src/opensc/src/sm/ |
| /src/opensc/src/libopensc/ |
| /src/opensc/src/pkcs11/../../src/common/ |
| /src/opensc/openpace/src/ |
| /usr/include/x86_64-linux-gnu/bits/ |
| /src/opensc/src/tests/fuzzing/../../../src/tools/ |
| /src/opensc/src/tests/fuzzing/../../tools/ |
| /src/opensc/src/libopensc/../../src/common/ |
Metadata section
This sections shows the raw data that is used to produce this report. This is mainly used for further processing and developer debugging.